iPhone Passwords Hacked In Minutes?
0So you store a lot of sensitive information on your iPhone, hoping that they will stay safe and secure on your device even if it gets stolen? Apparently, your sensitive information on your iPhone is not as secure as you think. A group of researchers in Germany have managed to reveal passwords stored in a locked iPhone without even having to crack its passcode. These researchers have found a way to get around Apple’s password management system, which only means hackers and thieves can too.
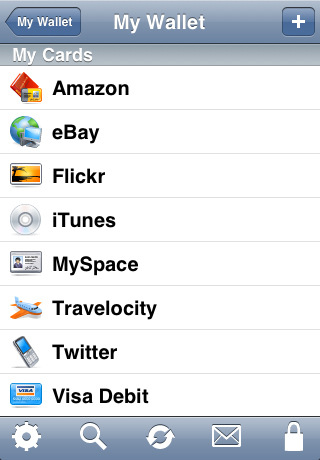
For this attack to work, the attacker needs to be in the possession of your iPhone. This hole is a major security headache for businesses and individuals storing sensitive credentials on their device:
As soon as attackers are in the possession of an iPhone or iPad and have removed the device’s SIM card… Control of an e-mail account allows the attacker to acquire even more additional passwords: For many web services such as social networks the attacker only has to request a password reset,
researchers claimed. The best case scenario is to not have any mission critical information available on iPhones. Corporate users want to be careful about the information they carry on their phones. Being vigilant when your iPhone is stolen helps too as Fraunhofer SIT explained:
Owner’s of a lost or stolen iOS device should therefore instantly initiate a change of all stored passwords… Additionally, this should be also done for accounts not stored on the device but which might have equal or similar passwords, as an attacker might try out revealed passwords against the full list of known accounts,
Trending iPhone, iPad apps:
No platform is perfect. As much as Apple fans want to believe that their devices are completely hack proof, it is always a smart idea to keep highly sensitive information away from your phone. Using encryption and other security tools further protects your data. Changing your passwords on a consistent basis is another way to make sure your accounts stay uncompromised over the long run.